There are so many ways to destroy data and sanitise storage media. But which one is best?
Well, there isn’t one correct answer for this. Rather, it depends on factors like:
- Sensitivity of data
- Type of device
- Whether you’ll use the device again or not
- Guidelines of prevalent data protection and sanitization standards
- And a lot more
In this guide, we’ve explained the differences between Purge, Clear, and Destroy – the three methods of data destruction under the NIST SP 800-800 standard.
Purge vs Clear vs Destroy. Read on to find out.
What is NIST SP 800-88 Media Sanitisation Standard?
NIST SP 800-88 is considered the golden standard for data sanitisation.
NIST stands for National Institute of Standards and Technology. It is a physical science laboratory and an agency of the US Department of Commerce.
The NIST 800-88 draws guidelines on how to erase data from a device such that it is non-recoverable. Under NIST 800-88, there are three categories of data destruction. These are Clear, Purge, and Destroy.
Read on to know the distinctions between the three types of data destruction.
Purge vs. Clear vs. Destroy
|
Purge |
Clear | Destroy | |
| Type of Sanitisation | Physical and logical sanitisation | Logical sanitisation | Physical sanitisation |
| Device Useful For | Floppy disks, hard disk drives, flash media | Floppy disks, disk drives, ATA hard drives | Floppy disks, hard disk drives, optical disks |
| Level of Protection | High | Moderate | Highest |
Besides the device in question, the sensitivity of the data is also a deciding factor for choosing whether to use Clear, Purge or Destroy. Here is a map of how the decision is made.
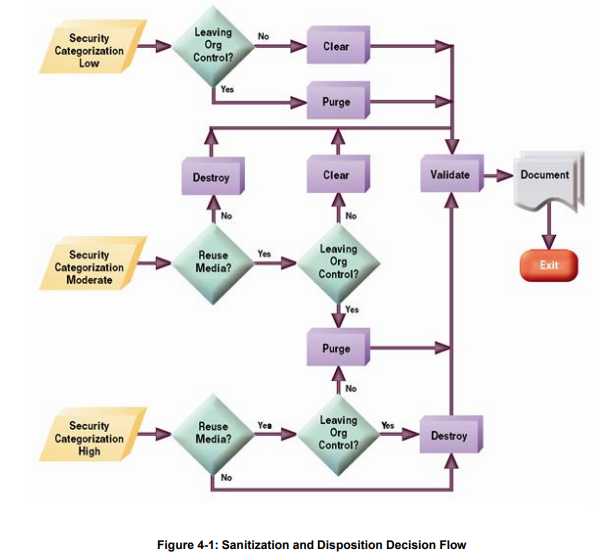
Image Source
What is Purge as defined in NIST 800-88?
Purge is a method of data sanitisation that uses both logical and physical methods to erase data. And the key requirement is that data recovery should become infeasible.
Under Purge, both overwriting and physical destruction are acceptable destruction techniques.
NIST Purge is usually conducted in a laboratory environment. Methods like overwriting, block erasure, and cryptographic erasure are applied under Purge. All of these are logical destruction methods. So the drive can be reused. Here are some methods used in the purge method.
- Overwriting: Either one or three overwriting passes are used to make data recovery impossible.
- Block Erase: Here, each block of the storage devices is deleted electrically. After one pass of the block erase method, binary 1s are applied over the user-addressable locations. Then block erasure is performed again.
- Cryptographic Erase: The Media Encryption Keys (MEKs) are sanitised. This makes the data non-retrievable.
Physical destruction techniques like shreddings, degaussing, and pulverising are also used. These render the device unusable. So technically the data is irrecoverable. But physical destruction techniques are not cost-efficient or environment friendly.
What is NIST Clear as defined in NIST 800-88?
NIST Clear is typically used with non-sensitive data. The method employs standard read and write commands to overwrite the data on the disk.
For data destruction to be effective, all the user addressable locations on a disk must be destroyed.
Overwriting can only be done if there is no physical damage to the disk. Overwriting, sometimes, isn’t possible on all areas of the device to be sanitised. That is why this technique is usually used with less sensitive data.
What is Destroy as defined in NIST 800-88?
The destroy method is often used as a last resort when purge and clear aren’t possible alternatives. It is also used when the data destruction verification with purge and clear techniques fail.
Under this method, the media isn’t considered fully sanitised unless data retrieval is proven to be infeasible using state-of-the-art laboratory techniques. Here are some techniques that are used to destroy devices.
- Disintegrate
- Pulverize
- Incinerate
- Melt
All of these techniques will completely destroy the device. Because of this, it is not possible to verify whether data destruction was successful.
Comparision Between Purge, Clear and Destroy?
Among purge, clear, and destroy, you have three equally robust data eraser techniques. When you know your erasure requirements better, then you can know which of these suits your purpose the best.
Purge vs Clear
| Purge | Clear |
| The purge method is used for more sensitive data. It is a dependable method of data destruction that is also verified. |
Clear is advised only for devices with non-sensitive data. This is because overwriting may not be possible on all areas of the disk. Data destruction is verified when using the clear technique as well. |
Purge vs Destroy
| Purge | Destroy |
|
Purge method is usually performed in a lab environment. You can also download software that will help you purge your drive. |
Destruction techniques are used only when purge and clear won’t work. Destroy also renders the device unusable. You need special equipment to effectively destroy the device. |
Clear vs Destroy
| Clear | Destroy |
| Clear uses single or triple overwriting passes to sanitise media. This, sometimes, doesn’t work on all parts of the storage media. |
Destruction techniques like shredding, degaussing, and melting are used depending on the type of device to sanitise. |
In the argument of purge vs clear vs destroy, the answer depends on the type of device to sanitise.
Let’s understand with the help of an example.
NIST 800-88 for ATA Hard Disk Drives
ATA, or Advanced Technical Attachment hard disks allow the disk to be connected to the motherboard of your PC. It can also perform basic input/output functions. Here is how you can sanitise the drive.
| Clear | Organizationally approved overwriting methods are used to sanitise the hard drive. |
| Purge |
|
| Destroy | You can pulverize, burn, melt, or disintegrate the device at a media destruction facility. |
If you’re choosing a software-based data wiping method, then you can sanitise the device in-house. Some software can also be automated.
So if you need to sanitise a device without too much of a hassle, then software-based methods, like purge and clear would be the best.
We hope this guide helped you understand NIST 800-88 in the context of Purge, Clear, and Destroy as three data destruction techniques.




